Skip to contentKakar Security Edition 2
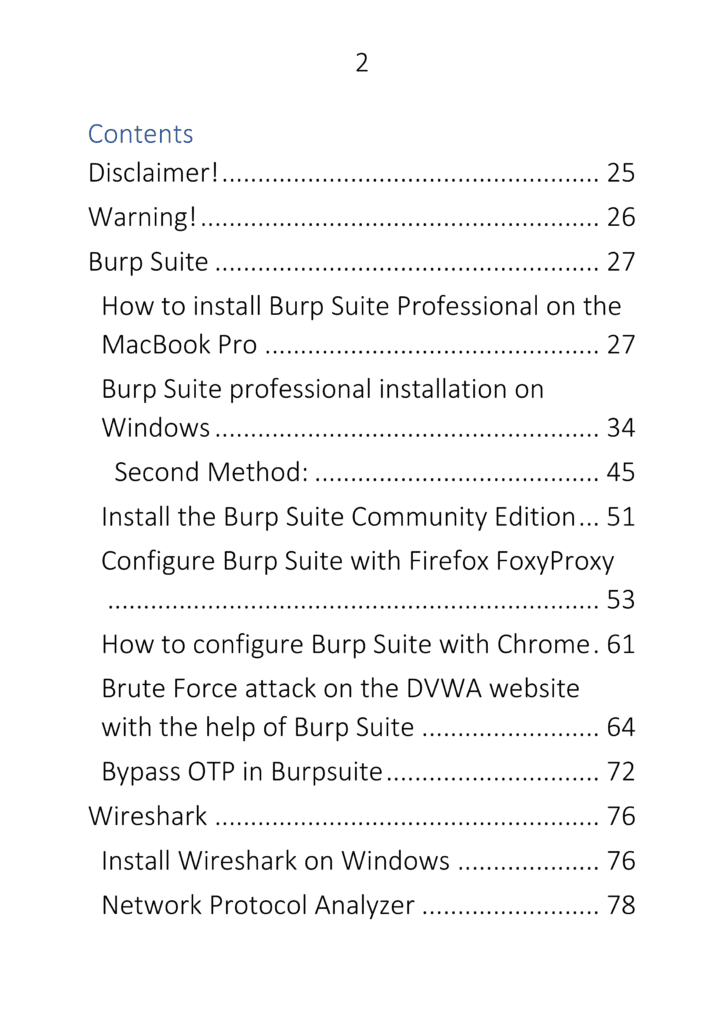
Contents
- Disclaimer!
- Warning!
- Burp Suite
- How to install Burp Suite Professional on the MacBook Pro
- Burp Suite professional installation on Windows
- Second Method:
- Install the Burp Suite Community Edition
- Configure Burp Suite with Firefox FoxyProxy
- How to configure Burp Suite with Chrome
- Brute Force attack on the DVWA website with the help of Burp Suite
- Bypass OTP in Burpsuite
- Wireshark
- Install Wireshark on Windows
- Network Protocol Analyzer
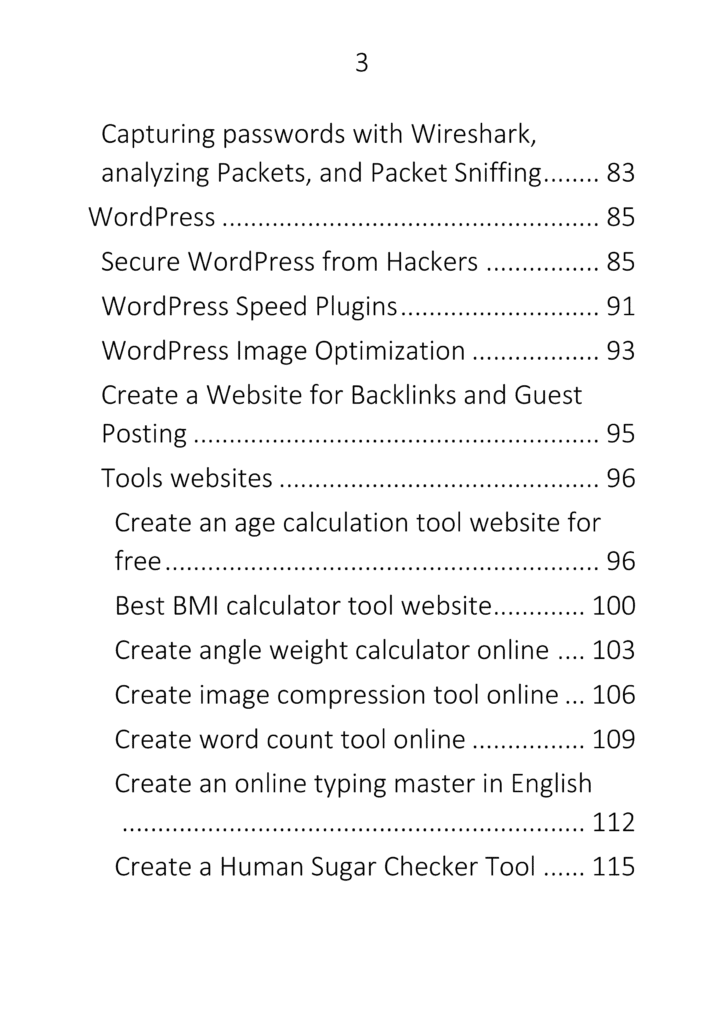
- Capturing passwords with Wireshark, Analyzing Packets, Packet Sniffing
- WordPress
- Secure WordPress from Hackers
- WordPress Speed Plugins
- WordPress Image Optimization
- Create a Website for Backlinks and Guest Posting
- Tools Websites
- Create an age calculation tool website for free
- Best BMI calculator tool website
- Create angle weight calculator online
- Create image compression tool online
- Create word count tool online
- Create an online typing master in English
- Create a Human Sugar Checker Tool
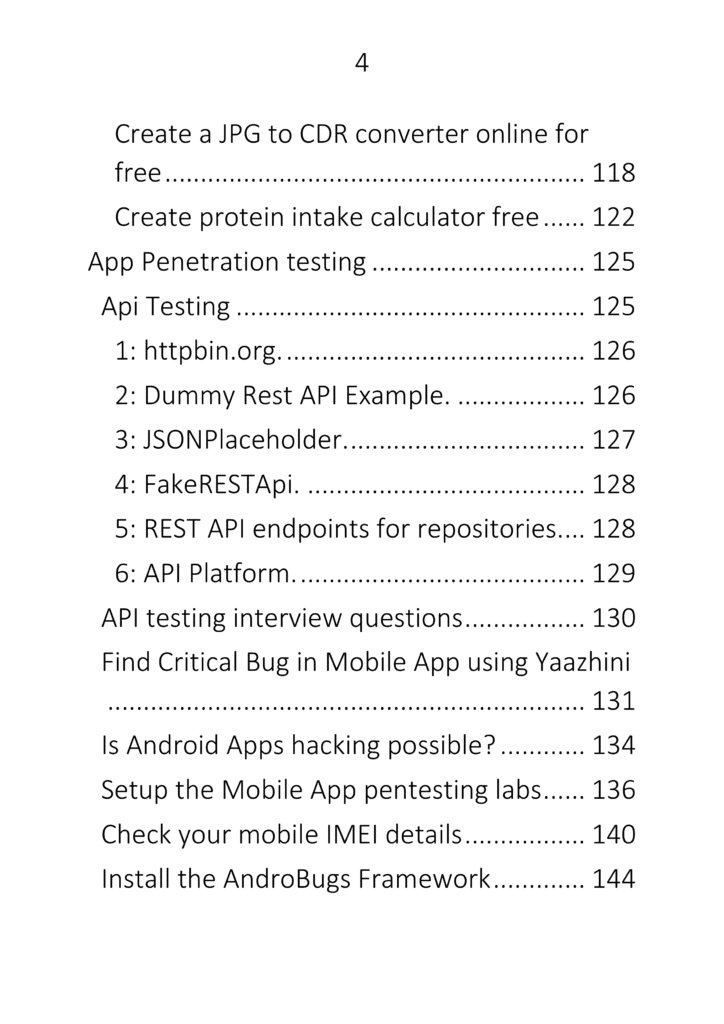
- Create a JPG to CDR converter online for free
- Create protein intake calculator free
- App Penetration Testing
- API Testing
- httpbin.org
- Dummy Rest API Example
- JSONPlaceholder
- FakeRESTApi
- REST API endpoints for repositories
- API Platform
- API testing interview questions
- Find Critical Bug in Mobile App using Yaazhini
- Is Android Apps hacking possible?
- Setup the Mobile App pentesting labs
- Check your mobile IMEI details
- Install the AndroBugs Framework
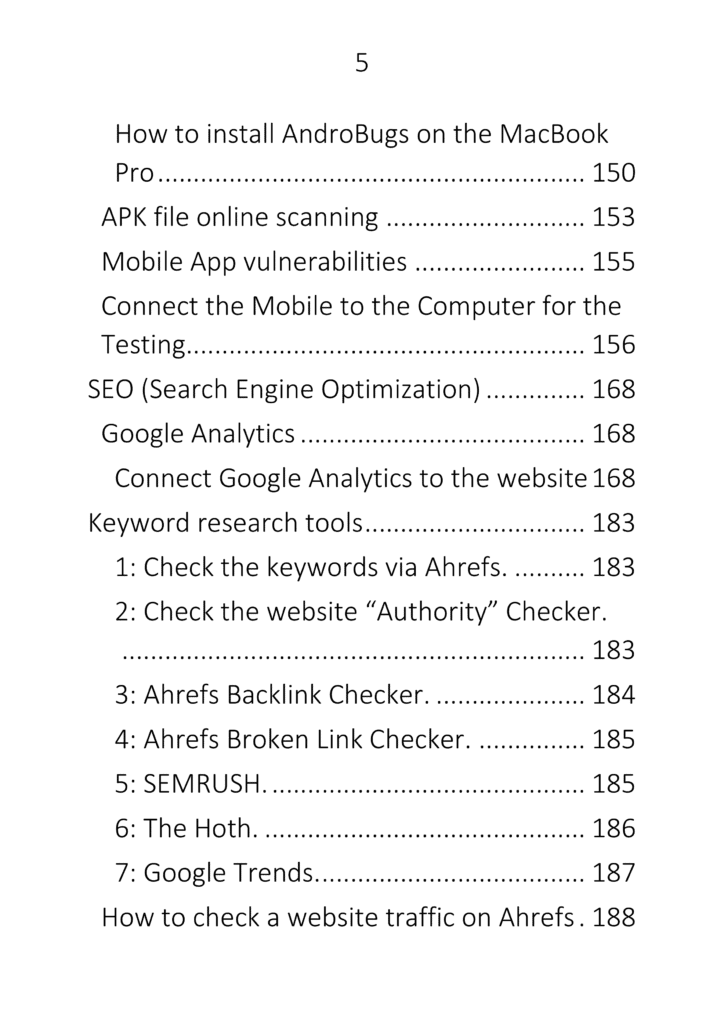
- How to install AndroBugs on the MacBook Pro
- APK file online scanning
- Mobile App vulnerabilities
- Connect the Mobile to the Computer for the Testing
- SEO (Search Engine Optimization)
- Google Analytics
- Connect Google Analytics to the website
- Keyword research tools
- How to check website traffic on Ahrefs
- Yandex – Add site to Yandex
- Bing Webmaster tools
- Technical SEO
- SEO Chrome Extensions
- URL optimization
- DuckDuckGo Indexing
- Audit website
- Add your website in Ahrefs
- Find low competition keywords
- Broken links
- Page load optimization
- Amazon SEO
- Google Search Console
- Plagiarism checker websites
- Backlinks
- Search Engine Submission
- SCADA (Supervisory Control and Data Acquisition)
- InTouch SCADA
- Automotive Security Testing
- Subdomain Enumeration
- Mobile Hacking
- PortSwigger Labs
- Bug Bounty
- ClickJacking
- Bug Bounty Vulnerabilities
- Open Redirect
- SSRF
- XSS
- XXE
- Bug Bounty Tips
- Hacking Search Engine
- Advanced Information Gathering Techniques
- RFI (Remote File Inclusion)
- DVWA Bug Hunting
- Wi-Fi Hacking
- Terraform
- Nmap (Network Mapping)
- Docker
- Digital Forensics
- Image Forensics
- Aerospace Hacking Tools
- Steganography
- Facebook OSINT
- Data Breach Checking
- Email Footprinting
- Google Hacking Database
- Website Malware Checker
- Nessus – Installation & Guide
- Programming (MySQL)
- Artificial Intelligence (AI)
- Cloud Platforms
- WampServer – Localhost WordPress
- LocalWP – WordPress
- XAMPP – WordPress
- Multipass
- DevOps → GitHub → Git
- Podman
- Satellites – ISRO GeoPortal
- Cryptocurrency – MetaMask
- RDP (Remote Desktop Protocol)
- SOC (Security Operations Center)
- Splunk
- Homebrew
- VMware Workstation (Mac)
- Data Analyst – Free Datasets
- Printers – HP LaserJet Error Fix
- Cisco – CCNA & Networking
- CISSP Topics
- pfSense + Firewall























1111